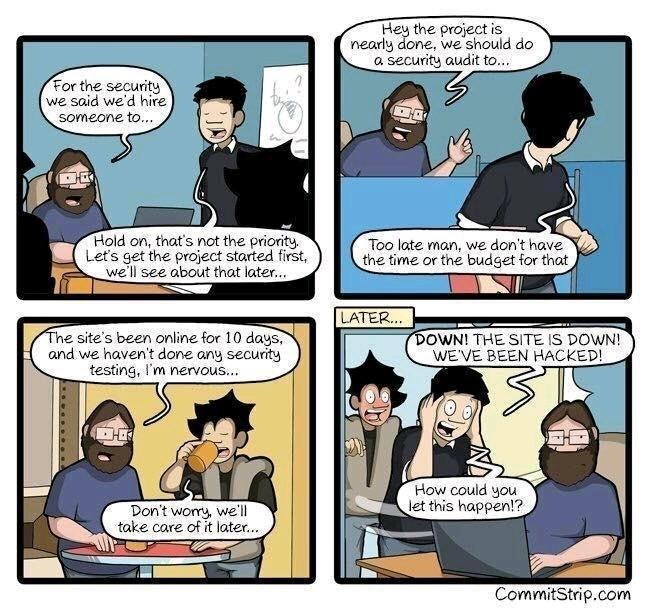
Fresh Snow Outside, Fresh Threats Inside: Practical Agentic AI Hardening
Saturday morning, blue skies, snow on the mountain and I’m sitting in this chair hacking away on Entra, HashiCorp Vault, Docker and Claude Code and OpenCode. What the is wrong with me? I thought after decade in cybersecurity, a masters degree and bunch of certifications that I’d be raking in the cash, out riding my…
Your AI Agent Is The Attacker – Claude, OpenCode – Threats and Security Designs
AI THREATS IN THE WILD In February 2026, the Cisco CX AI Tools team publicly flagged the popular OpenCode add-on oh-my-opencode after finding remote AI prompt injection in its installation guide. Their concern was not a theoretical bug but instead it was that an AI agent following the official instructions within source, could be manipulated…
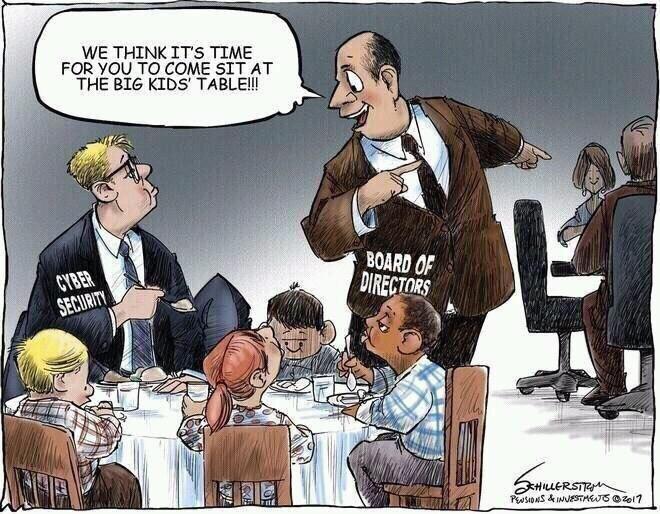
Microsoft Ignite 2025: AI Security – tl;dr but RTFM
Microsoft Ignite 2025: Mapping the M365 + Azure Attack Surface to the New AI Security Stack I spent the part of a week reading through the Microsoft Ignite 2025 announcements and honestly? The trend is interesting. AI this, AI that. Instead of the usual marketing fluff about “unified platforms” and “AI-powered everything,” Microsoft actually dropped…















