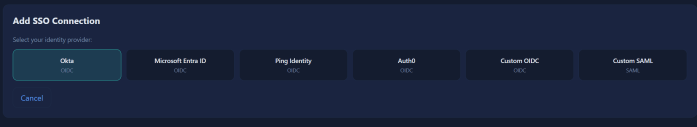
Overview Most security failures in multi-tenant SaaS aren't dramatic. They're quiet. A recycled database connection carries the wrong tenant's context into the next request. A JWT validator trusts a URL the attacker supplied in the token header. A logout endpoint clears the local session and leaves the identity provider session running. None of these look … Continue reading Building Enterprise SSO for my multi-tenant SaaS AI Agent platform
Tag: security
AI RED TEAMING – man-in-the-vector Attack & custom Tooling
Want deeper dives into AI vector embedding attack vectors? See more at Security Sandman. This article provides practical examples to assist red teams and security researches to find and exploit vulnerable AI systems using Vector Databases and even flow chaining tools. I've prototyped some simple tools to demonstrate the attack chain and later I'll finish … Continue reading AI RED TEAMING – man-in-the-vector Attack & custom Tooling
From Known to Unknown: Shifting Cybersecurity to Proactive AI Detection
Introduction Everyday, Cyber Security teams are faced with a chicken-and-egg problem to detect and contain bad things. As I'll discuss later in this article, it's my belief that cyber teams shift allocation of resources to engineering of unsupervised anomaly detections to hunt for broader and deeper unknown threats. Threat Intelligence Teams and Red Teams alike … Continue reading From Known to Unknown: Shifting Cybersecurity to Proactive AI Detection
CHANGE HEALTHCARE: ITS LITERALLY IN THE NAME
For cyber security folks, we're both horrified and laughing that a company named "Change Healthcare" who has stockpiles of marketing jargon for "Improving IT Security" also made the news for a cyber incident. As a cyber security professional by day and a partial owner and investor of a new medical business, this breach hits home … Continue reading CHANGE HEALTHCARE: ITS LITERALLY IN THE NAME