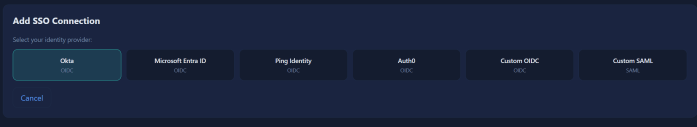
Overview Most security failures in multi-tenant SaaS aren't dramatic. They're quiet. A recycled database connection carries the wrong tenant's context into the next request. A JWT validator trusts a URL the attacker supplied in the token header. A logout endpoint clears the local session and leaves the identity provider session running. None of these look … Continue reading Building Enterprise SSO for my multi-tenant SaaS AI Agent platform
Author: @s3cs&man
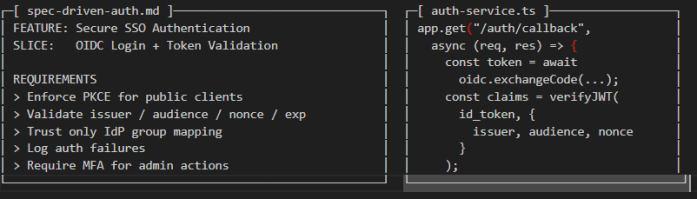
Mission-Critical IAM, Coding Agents and X-Agent Spec-Driven Collaboration
This article is about the uncomfortable truth that AI coding agents do and will continue to be used to write mission critical security code in products. Both now and in the future. And whether you like it or not and as much as I scrutinize prompt injection and over permissive agents, we need learn to … Continue reading Mission-Critical IAM, Coding Agents and X-Agent Spec-Driven Collaboration
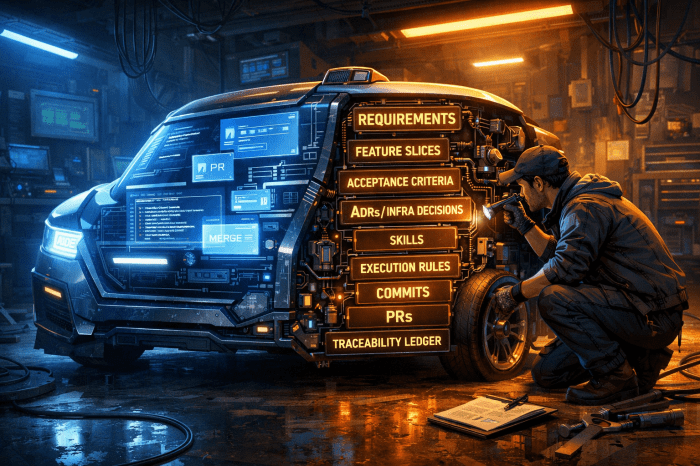
Kicking tires on “Spec” AI Development
Introduction Working on a side training project and improving the way I build with coding agents with the idea for better orchestrating, tracking and auditing agents work. I attended a Microsoft spec-driven "spek-kit" demo call where they discussed how to better organize these agents with the goal to make them more predictable. Buried beneath that … Continue reading Kicking tires on “Spec” AI Development
Fresh Snow Outside, Fresh Threats Inside: Practical Agentic AI Hardening
Saturday morning, blue skies, snow on the mountain and I'm sitting in this chair hacking away on Entra, HashiCorp Vault, Docker and Claude Code and OpenCode. What the is wrong with me? I thought after decade in cybersecurity, a masters degree and bunch of certifications that I'd be raking in the cash, out riding my … Continue reading Fresh Snow Outside, Fresh Threats Inside: Practical Agentic AI Hardening
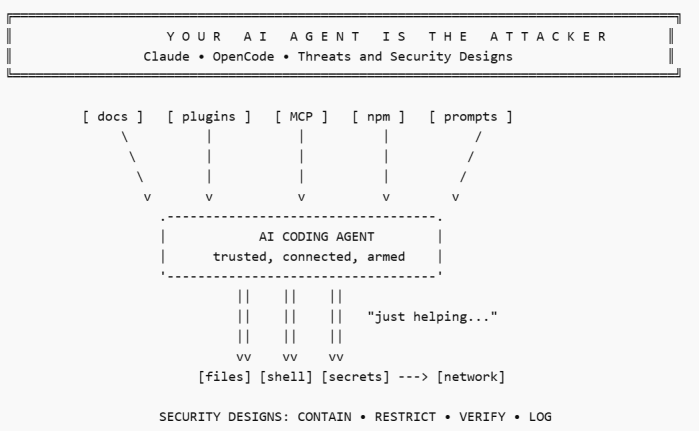
Your AI Agent Is The Attacker – Claude, OpenCode – Threats and Security Designs
AI THREATS IN THE WILD In February 2026, the Cisco CX AI Tools team publicly flagged the popular OpenCode add-on oh-my-opencode after finding remote AI prompt injection in its installation guide. Their concern was not a theoretical bug but instead it was that an AI agent following the official instructions within source, could be manipulated … Continue reading Your AI Agent Is The Attacker – Claude, OpenCode – Threats and Security Designs
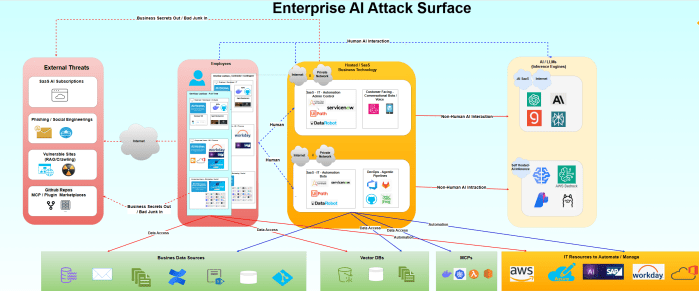
Microsoft Ignite 2025: AI Security – tl;dr but RTFM
Microsoft Ignite 2025: Mapping the M365 + Azure Attack Surface to the New AI Security Stack I spent the part of a week reading through the Microsoft Ignite 2025 announcements and honestly? The trend is interesting. AI this, AI that. Instead of the usual marketing fluff about "unified platforms" and "AI-powered everything," Microsoft actually dropped … Continue reading Microsoft Ignite 2025: AI Security – tl;dr but RTFM
Seeing the AI-Security Forest Through the Trees
A strategic look at adoption, exposure and what to do next ... https://videopress.com/v/jbURi21D?resizeToParent=true&cover=true&preloadContent=metadata&useAverageColor=true Executive take AI adoption is rising fastest in Software Engineering, Marketing/Sales, and Service/Customer Ops, while Finance/HR/Legal are catching up more cautiously. Globally, we've seen exponential innovation and patent filing of AI solutions. Exponential AI Innovation = Growing Attack Surface Source: Stanford "State … Continue reading Seeing the AI-Security Forest Through the Trees
Is Claude Code Secure? Let’s Find Out!
Vulnerable Plugin + MCP Enumeration https://videopress.com/v/hAWQ87ND?resizeToParent=true&cover=true&preloadContent=metadata&useAverageColor=true TL&DR Claude Code didn’t invent most of the security problems discussed in this article but it will make them faster, louder and easier to repeat. As I rush to use AI myself, I realize the attack surface is widening in ways that follow classic software supply chain weaknesses: Unsigned … Continue reading Is Claude Code Secure? Let’s Find Out!
Anthropic’s Security Layers Explained: The Good, Bad & Ugly
Can you secure the Anthropic SaaS cloud platform? The answer, sorta, kinda, maybe. This article is intended for architects and managers. Low level embedded security analysis is in the works for next week in another article. Let me say ahead of time, huge shout out to Anthropic, I personally respect the company a ton and … Continue reading Anthropic’s Security Layers Explained: The Good, Bad & Ugly
AI RED TEAMING – man-in-the-vector Attack & custom Tooling
Want deeper dives into AI vector embedding attack vectors? See more at Security Sandman. This article provides practical examples to assist red teams and security researches to find and exploit vulnerable AI systems using Vector Databases and even flow chaining tools. I've prototyped some simple tools to demonstrate the attack chain and later I'll finish … Continue reading AI RED TEAMING – man-in-the-vector Attack & custom Tooling